Expose your attack surface. Stop what's exploitable.
Continuous discovery for Internet-facting assets, high-fidelity scanning, and AI-driven risk prioritization. Map your complete external footprint in minutes.

Complete Attack Surface
Protection in 4 Steps
From discovery to real-time alerting, FullHunt provides continuous attack surface management that scales with your organization.
Discover
Cloud-distributed engines automatically discover and map your entire external attack surface in minutes, including domains, subdomains, IPs, and cloud assets.
Monitor
24/7 continuous monitoring tracks every change across your attack surface, detecting new assets, configuration drifts, and potential exposures in real-time.
Detect
Automated scanning identifies thousands of vulnerabilities across your assets, with runtime validation ensuring zero false positives and accurate risk assessment.
Alert
Instant notifications through your preferred channels (Slack, Teams, SIEM) whenever critical risks or exposures are identified, enabling immediate response.
Every attack surface capability,
unified in one engine.
The FullHunt ASM platform is the functional core behind every tier. Discover assets, detect exposures, monitor threats, and act.
Explore the Platform →
The internet's largest
ASM database,
via REST.
Query millions of hosts in milliseconds. Built for threat hunting, pipeline enrichment, and SecOps automation at any scale.
{
"host": "legacy-vpn.acme-corp.com",
"ip_address": "185.220.101.47",
"is_live": true,
"network_ports": [443, 8443, 4433],
"technologies": ["Pulse Secure 9.1R3", "Apache 2.4.49"],
"vulnerabilities": [
{
"cve_id": "CVE-2021-22893",
"cvss_v3_score": 10.0,
"severity": "CRITICAL",
"is_kev": true,
"epss_score": 0.974,
"has_public_exploit": true,
"exploit_count": 14
}
],
"metadata": { "last_seen": "2026-03-08T14:22:00Z", "validated": true }
}
Built for those who serve many.
Run client portfolios at scale or embed attack surface intelligence directly into your product. FullHunt has the infrastructure layer for both.
One dashboard.
Every client's attack surface.
Stop context-switching between client tools. FullHunt gives MSSPs full tenant isolation, automated discovery, and consolidated risk reporting, so your team can protect more without growing headcount.
The data infrastructure behind FullHunt, available to license.
Embed internet-scale ASM
directly into your product.
License FullHunt's scanning infrastructure and data feeds. Power your risk engine, threat scoring, or exposure workflows with the same data that drives the FullHunt platform, without the years it takes to build it yourself.
FullHunt at the center of your security stack.
Intelligence flows outward from FullHunt into every tool your team runs: SIEM, SOAR, AI agents, ticketing, and beyond. One hub, every direction.
AI agents that understand your attack surface.
Connect Claude, Copilot, or any MCP-compatible AI agent directly to FullHunt's live data. Ask natural language questions, trigger scans, and surface risk. No glue code required.
Ship ASM capabilities under your own brand.
License FullHunt's scanning engine and data feeds to power the exposure management or threat intelligence features inside your product, without building the infrastructure yourself.
Constantly Evolving Intelligence
Fingerprints across frameworks, CMSs, CDNs, and web services. Continuously updated.
Version-aware detection across network devices, cloud APIs, and software stacks.
PoC and weaponized exploit database updated in real-time and mapped to live assets.
Vulnerability and Exploit Intelligence
Curated security research and real-time exploit tracking, delivered directly to your console and APIs so you act before attackers do.
Everything you need to own your attack surface.
Discover, monitor, scan, and act. All from one platform. No stitching together tools. No coverage gaps.

Internet-Scale Discovery
Map every external-facing asset: subdomains, IPs, cloud services, shadow IT. Continuously updated as your footprint changes.

Continuous Monitoring
Track changes, new services, and configuration drift in real time. Alerts fire the moment your attack surface shifts.

High-Fidelity Scanning
Runtime-validated vulnerability checks across thousands of signatures. High signal, low noise, no manual triage.

Vulnerability and Exploit Intelligence
CVEs mapped to your live surface with exploitability weighting. Curated PoC tracking so you fix what attackers will use first.

Dark Web Monitoring
Credential leaks, breached accounts, typosquatting, and phishing domains, detected and tied back to your monitored assets.

Third-Party Risk
Extend visibility to vendors and subsidiaries with scoped monitoring, risk scoring, and consolidated reporting.
Continuously Updated Vulnerability Checks
Every asset on your attack surface is tested for known CVEs, misconfigurations, and exposed services. New checks are added as vulnerabilities are disclosed.
The First-Ever
External Assets Monitoring Technology
FullHunt built the first enterprise-level framework for continuously monitoring the External Attack Surface for changes and exposure, then kept building. What started as a novel approach has evolved into the most comprehensive attack surface intelligence platform used by security teams worldwide.
Solving Attack Surface Management at Scale

The Start
FullHunt started as a project to solve a security challenge that all companies face today: Understanding the current exposure and performing continuous monitoring.
The Growth
FullHunt grew from a community project to become one of the leading Attack Surface Management platforms in the market.

The Expand
FullHunt now provides a suite of products to help build and mature your security program, including Continuous Attack Surface Management, DarkWeb Monitoring, Third Party Risk Management, Data Intelligence APIs, and Global Internet Space Scanning. Everything is powered by the FullHunt technology.


FullHunt Integrates With All Workflows And Playbooks
FullHunt provides a comprehensive set of APIs and integrations to help you automate your security workflows and playbooks.
Use some of the following integrations natively within the FullHunt Platform
Two ways to access FullHunt intelligence.
From hands-on investigation to a fully managed attack surface program, built for every level of security operation.
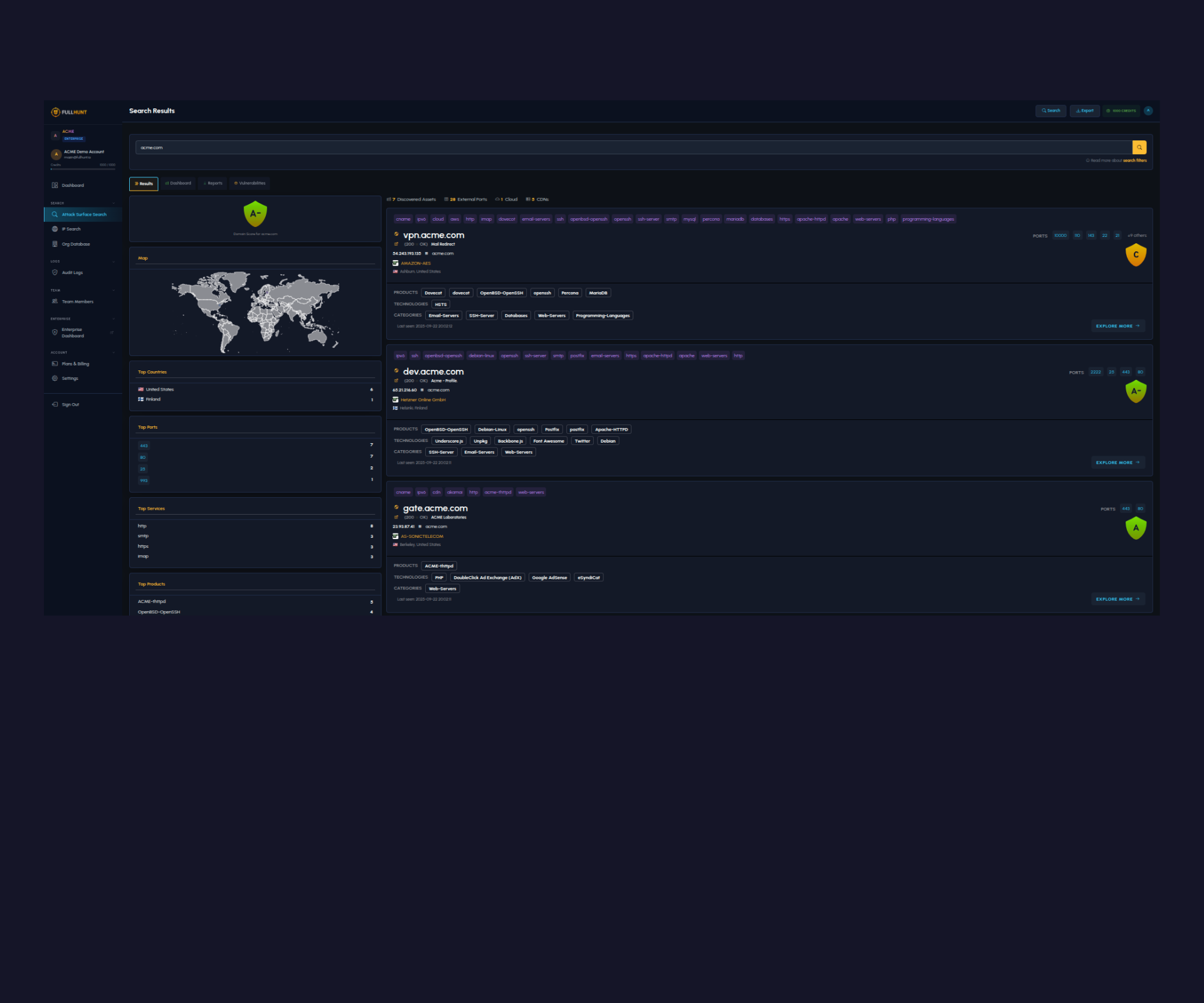
FullHunt Console
For Security Vendors & Security Automation
Direct access to FullHunt's internet-scale attack surface database. Search hosts, domains, and IPs. Fingerprint technologies, query open ports and exposed services, through the console or the REST API.
Start for Free
FullHunt Enterprise
For Enterprises & MSSPs
A continuous ASM program, not just a tool. FullHunt maps your entire external perimeter, monitors it persistently, and maps vulnerabilities to live assets, prioritized by real-world exploitability.
Request a DemoReady to expose your attack surface?
Join security teams using FullHunt to discover, monitor, and secure their external infrastructure.






