External Attack Surface Management
Continuous discovery, validated vulnerabilities, and dark web monitoring. No false-positive noise.

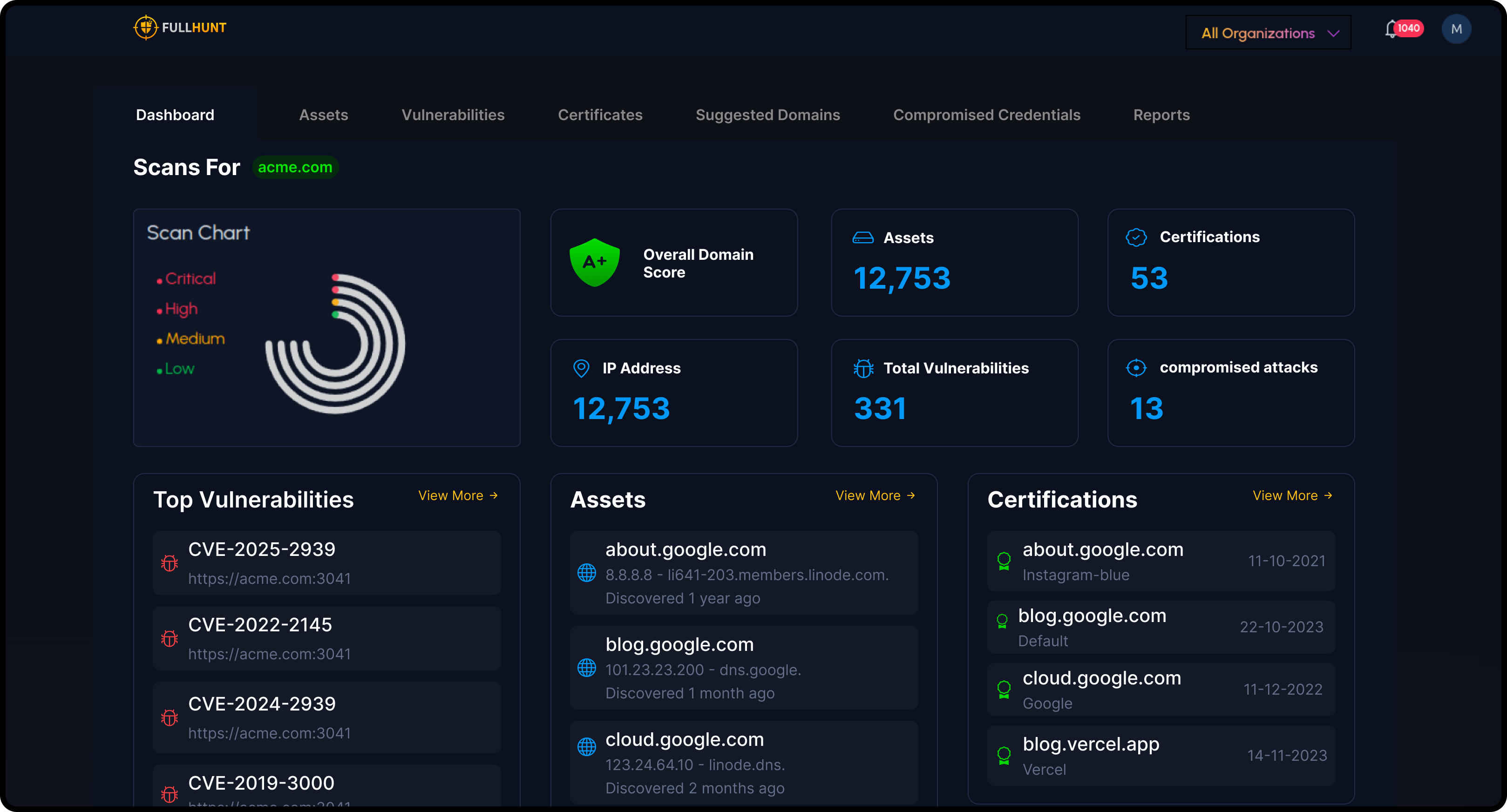
Map your entire external perimeter. Keep it current.
FullHunt discovers domains, subdomains, IPs, cloud services, and tech stacks at internet scale, then monitors them continuously. Shadow IT and forgotten assets surface automatically. No agents required.
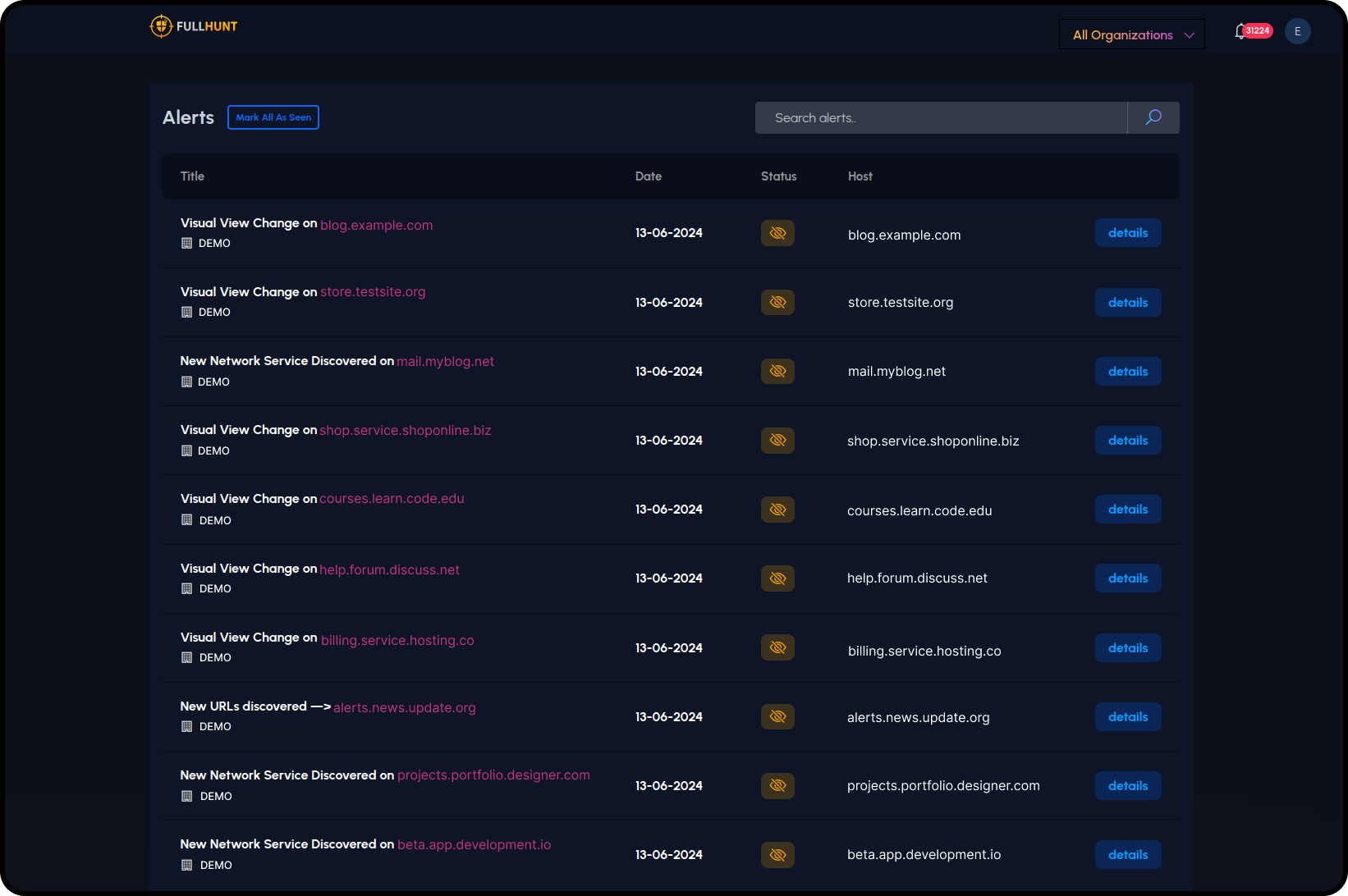
Know the moment your attack surface changes.
Real-time alerting on visual changes, new services, new URLs, and configuration drift. Every change is logged and attributed.
- — Visual change detection
- — New network services
- — New URLs & endpoints
- — Configuration drift alerts
Runtime-validated checks. Not guesswork.
Thousands of security checks run against live assets. Every finding is confirmed at runtime. False positives get cut before they reach your team.
- — 4,000+ vulnerability checks
- — Runtime validation for each finding
- — EPSS & KEV enrichment built-in
- — Public exploit correlation
- — Asset scoring by exploitability
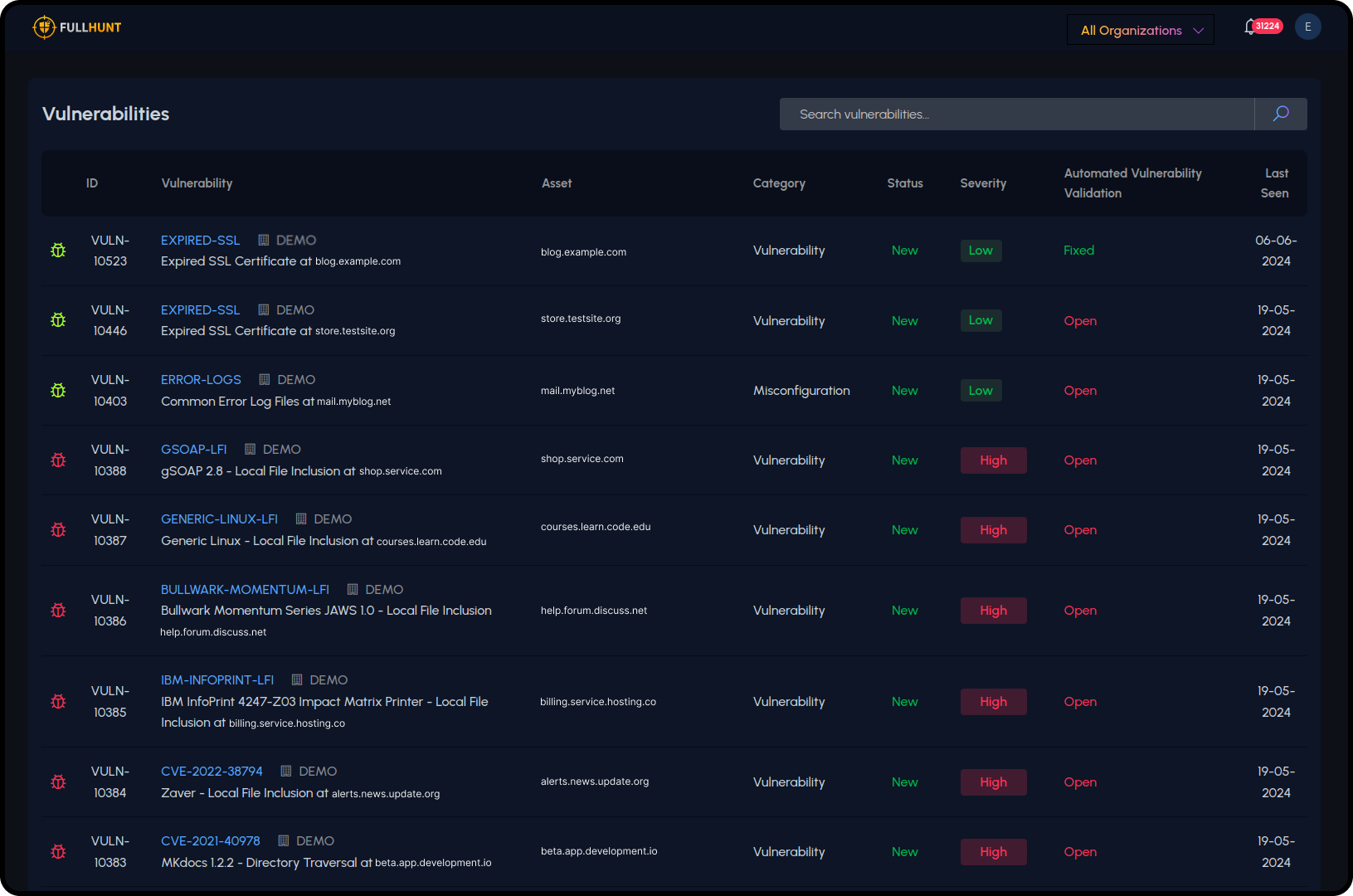
Every vulnerability validated. Prioritized by real-world risk.
4,000+ security checks run against live assets with runtime validation. Findings are enriched with exploit context, EPSS, and KEV data.
- — Expired SSL certificates
- — Misconfigurations
- — Local file inclusion
- — CVE-specific checks
Every CVE enriched with exploit context.
EPSS scores, CISA KEV status, and 100,000+ tracked public exploits are layered onto your attack surface. No separate tool. No manual lookups.
GitHub, Exploit-DB, security research. Indexed and correlated daily.
ML-driven exploit prediction updated daily. Prioritize by likelihood, not just CVSS.
CISA Known Exploited Vulnerabilities mapped to your assets. Alerts on match.
Smaller Patch Queues
Focus on exploited and exploitable vulnerabilities. Cut patch queues by 70%+ with exploit-aware prioritization.
Faster MTTR
Automated enrichment eliminates manual CVE research. Teams start remediation with full context from the start.
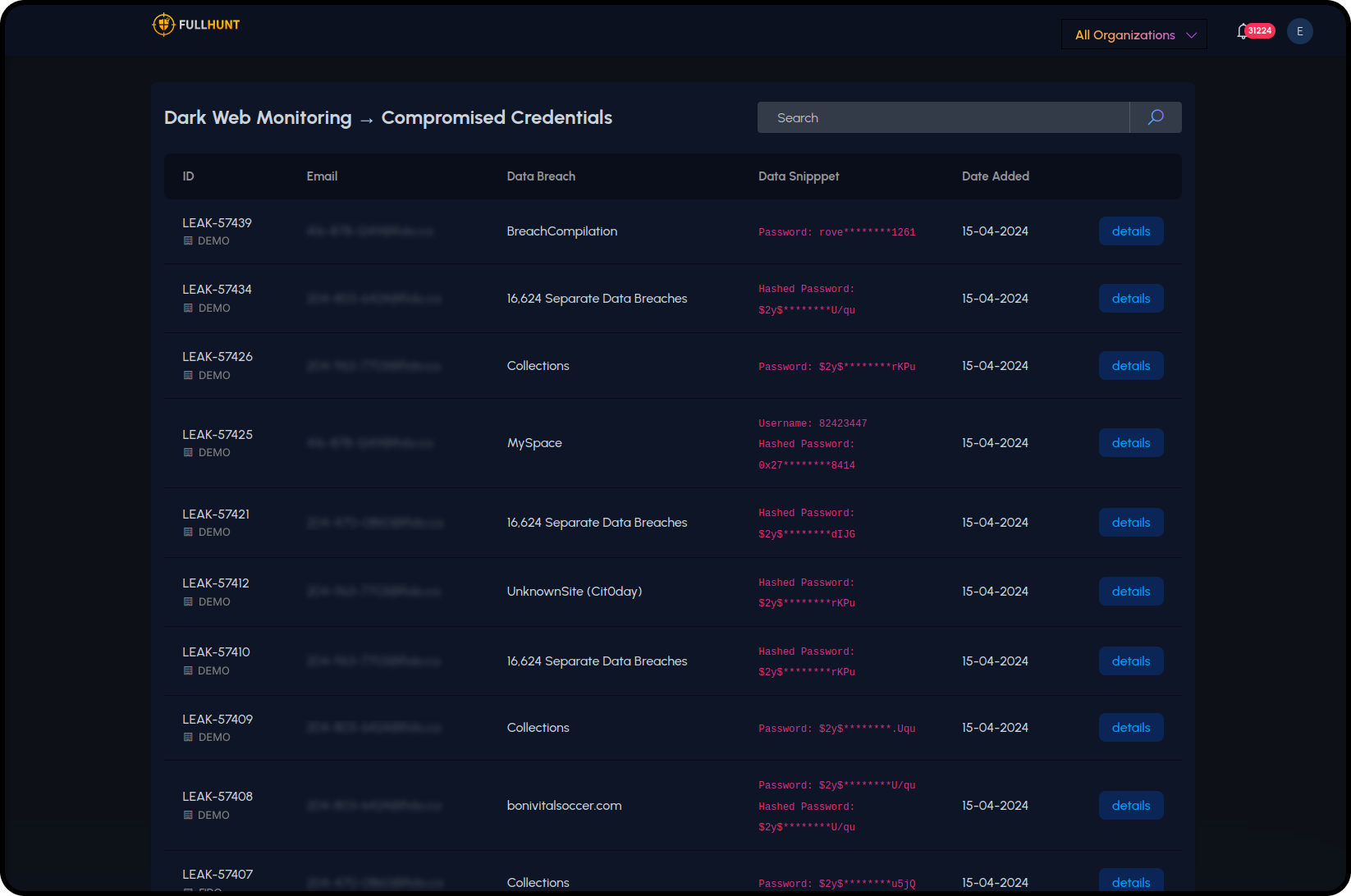
Visibility beyond your own perimeter.
Credential leaks, breached accounts, and dark web mentions tied to your domains. Vendor and subsidiary exposure monitored continuously.
- — Compromised credential alerts
- — Typosquatting & phishing lookalikes
- — Third-party vendor exposure scoring
- — Subsidiary attack surface monitoring
Discover → Monitor → Validate → Integrate
A continuous cycle. No agents, no infrastructure. Operational in under 30 minutes.
Discover
Map your complete external footprint: domains, IPs, cloud, technologies, at internet scale.
Monitor
Track changes, new services, and configuration drift 24/7 with real-time alerts.
Validate
Runtime checks confirm real exploitability. EPSS and KEV enrich every finding.
Integrate
Push findings to Splunk, XSOAR, Jira, Slack, and more.
Why teams choose Enterprise ASM
Continuous, Not Point-in-Time
No blind spots between assessments. Discovery and monitoring run 24/7.
High Signal, Low Noise
Runtime validation cuts false positives. Your team works on real issues.
Fits Your Workflow
Findings flow into the tools your team already uses. No context switching.
Fast Time to Value
Operational in under 30 minutes. See your entire external footprint in seconds.
Enterprise-ready from day one
SSO & RBAC
Enterprise auth and role-based access built in
30-Min Setup
No infrastructure to deploy
Zero Agents
Outside-in visibility, no perf impact
Scales to 400K
Startups to Fortune 500
Ready to secure your attack surface?
Talk to our team or start a free trial.