Enterprise ASM
Continuous monitoring, vulnerability scanning, dark web intelligence, and SOC integrations for security teams managing real attack surfaces.
14-day trial available for qualified organizations
Starting at $19,000 USD/year
per deployment
in real time
onboarding
monitoring

Pricing based on your scope
Enterprise ASM is quoted per organization. Three factors shape your price.
Everything included. No upsells.
Every Enterprise ASM deployment ships with the complete stack.
Discovery & Monitoring
- Attack surface discovery (subdomains, IPs, cloud)
- Continuous exposure monitoring with change alerts
- Technology fingerprinting
- Certificate & SSL monitoring
- URL discovery & web crawling
Vulnerability Intelligence
- Thousands of vulnerability checks, zero false positives
- 100K+ exploits correlated in real time
- EPSS & KEV enrichment
- Prioritization by exploitation & criticality
- 1-day exploit detection
- Per-asset risk scoring
Dark Web Intelligence
- Compromised credentials & infostealer detection
- Typosquatting & brand impersonation
- Phishing infrastructure monitoring
- Nation-scale global search
- Human-led exploitation validation
Enterprise Scanning
- External attack surface threat identification
- Third-party vendor risk assessment
- DNS security & dangling record detection
- Cloud misconfig detection (S3, APIs, etc.)
- SSL/TLS chain validation & cipher analysis
Integrations
- SIEM: Splunk, Sumo Logic
- SOAR: XSOAR, FortiSOAR, Mindflow
- Ticketing: Jira, ServiceNow
- Chat: Slack, Microsoft Teams
- Custom webhooks & full REST API
- CSV, JSON, PDF scheduled exports
Reporting & Support
- Advanced analytics dashboard
- Executive summaries & compliance docs
- Trend analysis & historical data
- Dedicated team with 24/7 support
- Custom SLA & SSO access
- Guided onboarding in <30 min
See what you get
A closer look at the capabilities powering your security team.
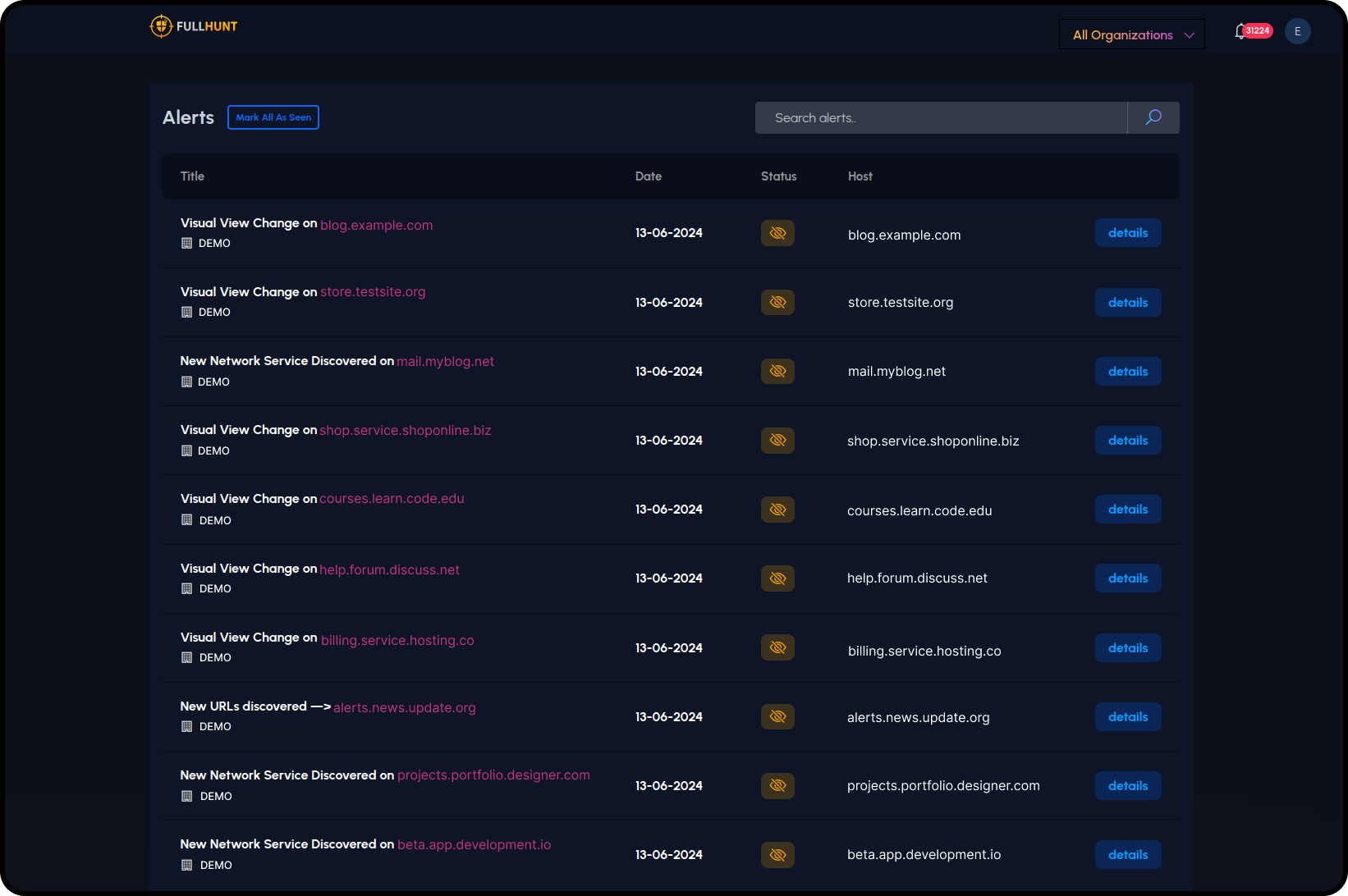
Real-Time Exposure Detection
Continuous monitoring detects configuration drift, new services, and exposed assets the moment they appear. Automated alerts route to your team via Slack, Teams, or any webhook.
- Automated change detection across your entire attack surface
- Instant alerts for new subdomains, open ports, and misconfigs
- Historical diffing to track how your surface evolves
- Integration with SIEM, SOAR, and ticketing systems
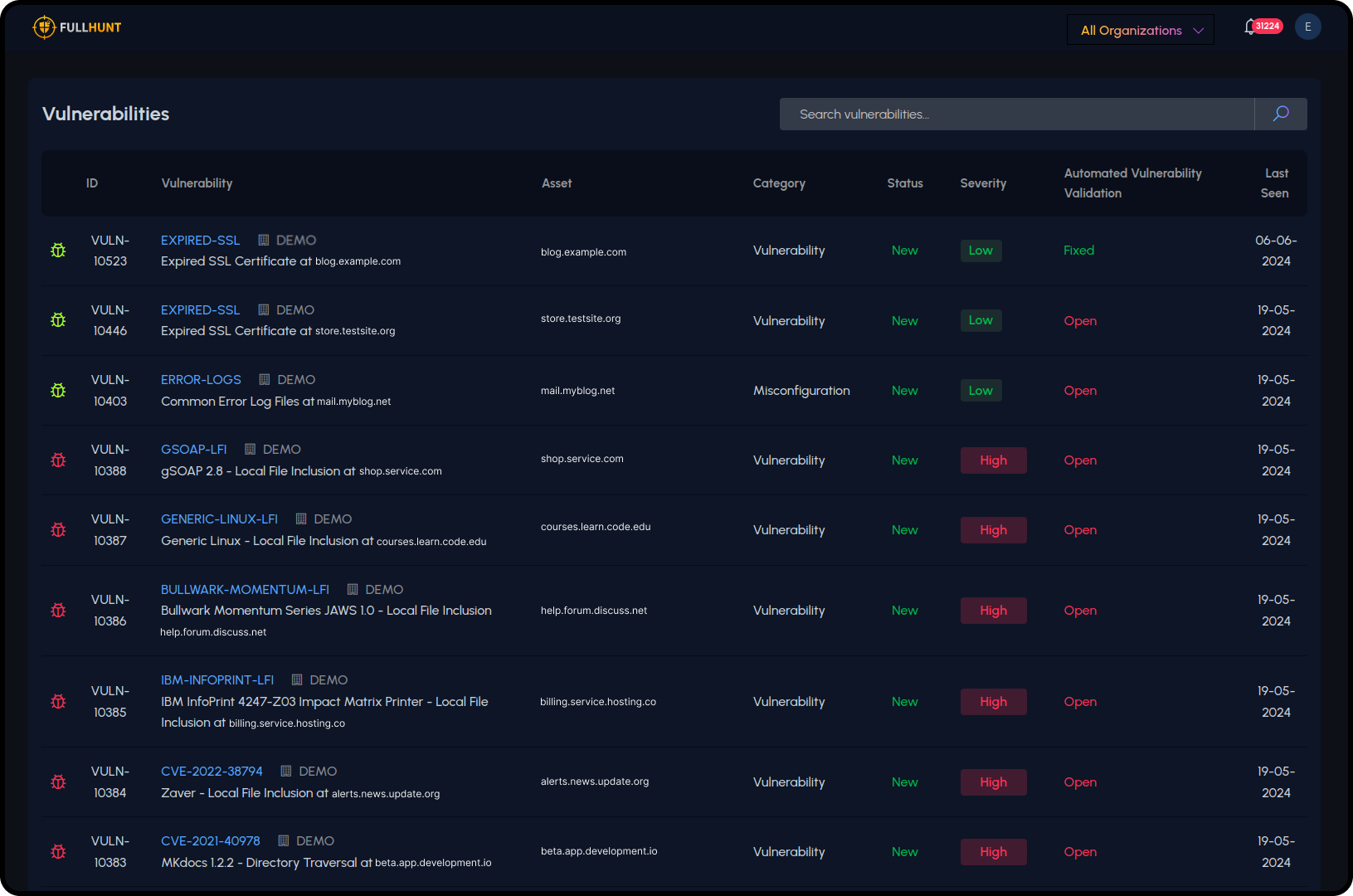
Vulnerability Scanning & Validation
Thousands of vulnerability checks with runtime validation ensure zero false positives. Every finding is correlated against 100K+ known exploits and scored by real-world exploitability.
- EPSS and KEV enrichment for every vulnerability
- Prioritization by public exploitation and asset criticality
- 1-day exploit detection as new CVEs drop
- Exportable reports with remediation guidance
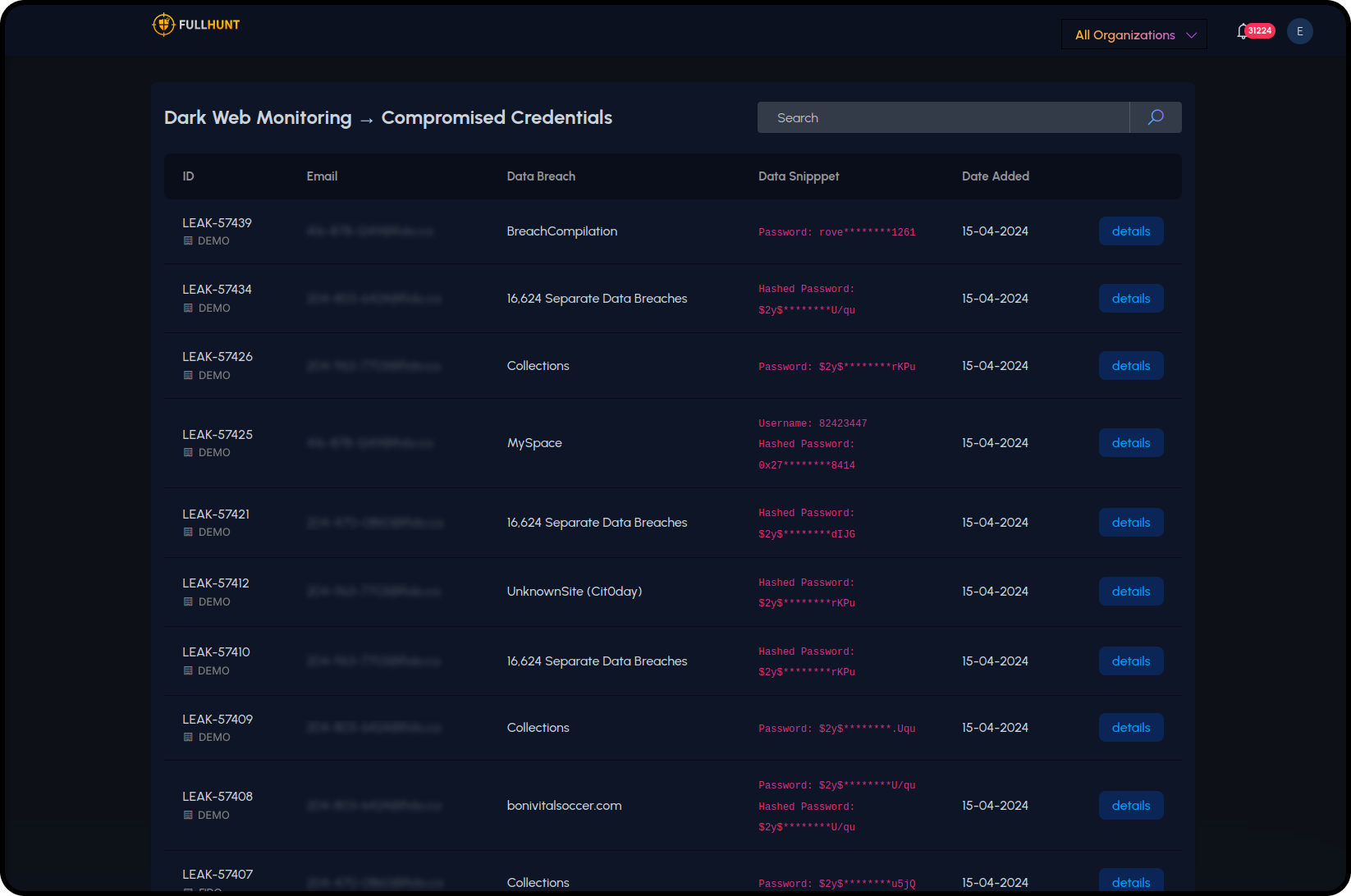
Dark Web & Threat Intelligence
Monitor the dark web for compromised credentials, infostealer logs, brand impersonation, and phishing infrastructure targeting your organization. All correlated against your attack surface.
- Employee credential breach monitoring
- Infostealer detection across dark web markets
- Typosquatting and phishing site detection
- Human-led exploitation validation for critical findings
Full capabilities breakdown
Every Enterprise ASM deployment includes the full platform. No feature gating.
| Capability | Details |
|---|---|
| Discovery & Monitoring | |
| Attack Surface Discovery | Advanced + continuous. Subdomains, IPs, cloud assets (AWS, Azure, GCP, Alibaba, Oracle). |
| Continuous Exposure Monitoring | 24/7 real-time monitoring with automated alerts on configuration drift and change detection. |
| Technology Fingerprinting | Thousands of technology signatures identified and tracked. |
| Certificate Monitoring | TLS/SSL certificate tracking and expiration alerting. |
| URL Discovery & Crawling | Automated web crawling to discover exposed endpoints and resources. |
| Vulnerability & Exploit Intelligence | |
| Vulnerability Scanning | Thousands of checks with runtime validation. Zero false positives. |
| Exploit Correlation | 100K+ exploits correlated against your attack surface in real time. |
| EPSS & KEV Enrichment | Exploit prediction scoring and known exploited vulnerability tracking. |
| Vulnerability Prioritization | Scored by public exploitation, EPSS, and asset criticality. |
| Asset Risk Scoring | Per-asset scores derived from exploitable vulnerabilities and exposure data. |
| 1-Day Exploit Detection | Detection of newly published exploits against your surface. |
| Dark Web & Threat Intelligence | |
| Compromised Credentials | Employee breach monitoring, infostealer detection, and dark web leaks. |
| Typosquatting Detection | Automated detection of domain lookalikes targeting your brand. |
| Phishing Infrastructure | Monitoring for phishing sites and infrastructure impersonating your organization. |
| Global Search | Nation-scale search across the full FullHunt intelligence database. |
| Human-Led Exploitation | Expert-driven validation of critical findings. |
| Enterprise Scanning | |
| External Attack Surface Threats | Identification of internet-facing risks and exposed services. |
| Third-Party Vendor Risk | Scan vendors and suppliers to assess supply chain exposure. |
| DNS Security | Full DNS validation including dangling records, zone issues, and misconfigurations. |
| Cloud Security Misconfigurations | Detection of exposed buckets, open APIs, and cloud service misconfigs. |
| SSL/TLS Validation | Full certificate chain validation, protocol version checks, and cipher analysis. |
| Integrations & Exports | |
| SIEM (Splunk, Sumo Logic) | Native integrations with automated data forwarding. |
| SOAR (XSOAR, FortiSOAR, Mindflow) | Native playbook integrations for automated response. |
| Ticketing (Jira, ServiceNow) | Automated ticket creation and bi-directional sync. |
| Chat (Slack, Teams) | Real-time alert routing to team channels. |
| Custom Webhooks | Event-driven webhooks for any downstream system. |
| Exports | CSV, JSON, and PDF exports with scheduled delivery. |
| Reporting & Dashboards | |
| Platform Dashboard | Advanced analytics dashboard with drill-down views. |
| Vulnerability Reports | Prioritized reports with remediation guidance. |
| Executive Summaries | C-level reports with trend analysis and risk posture. |
| Compliance Documentation | Pre-formatted reports for audit and compliance workflows. |
| Trend Analysis | Historical data comparison and attack surface growth tracking. |
| Support & Scale | |
| Support | Dedicated team, 24/7 availability, assigned technical account manager. |
| Onboarding | Guided onboarding in less than 30 minutes. Full team training. |
| Monitored Assets | Up to 400K assets per deployment. |
| User Seats | Custom team access with SSO support (SAML, OIDC, Google, Okta). |
| SLA | Custom enterprise SLA with defined response times. |
| API Access | Full Enterprise API with unlimited searches and results. |
Ready to see it in action?
Most teams are fully onboarded in under 30 minutes. No agents to install, no infrastructure to provision.
Specialized programs
Custom programs for specific use cases and partnership requirements.
MSSP
Multi-tenant monitoring for managed security providers serving multiple client attack surfaces.
Contact sales →Reseller
Include FullHunt in your bids and service packages. Partner pricing and co-branding available.
Contact sales →National CERT
Protect and monitor your nation's external attack surface. Scales to millions of assets.
Contact government team →Technology Partner
Build connectors and integrations that extend the FullHunt platform for your customers.
Contact engineering →Got questions?
Everything you need to know about Enterprise ASM deployment and billing.
Is there a free trial?
Yes. Qualified organizations can get a 14-day trial of the full Enterprise ASM platform. Request a demo and our team will set it up.
How long does onboarding take?
Most teams are fully onboarded in under 30 minutes. No agents, no infrastructure changes. Add your domains and start seeing results immediately.
What's the minimum contract?
We offer monthly and annual agreements. Annual contracts include a discount. Multi-year terms are available for larger deployments.
How many assets can I monitor?
Standard deployments cover up to 400,000 assets. For larger-scale monitoring (national CERTs, large enterprises), talk to our team about custom capacity.
Does Enterprise ASM use credits?
No. Enterprise ASM uses asset-based pricing, not credits. You're billed based on the scope of your monitored attack surface, not individual API calls.
What integrations are supported?
Splunk, Sumo Logic, Cortex XSOAR, FortiSOAR, Mindflow, Jira, ServiceNow, Slack, Microsoft Teams, and custom webhooks. We also provide a full REST API.
