Complete Attack Surface Visibility for Enterprise Security Teams
Continuous discovery, dark web monitoring, vulnerability intelligence, and agentic AI, unified for in-house security teams that need full coverage without the noise.

Map your entire external perimeter. Keep it current.
FullHunt discovers domains, subdomains, IPs, cloud services, and tech stacks at internet scale, then monitors them continuously. Shadow IT and forgotten assets surface automatically.
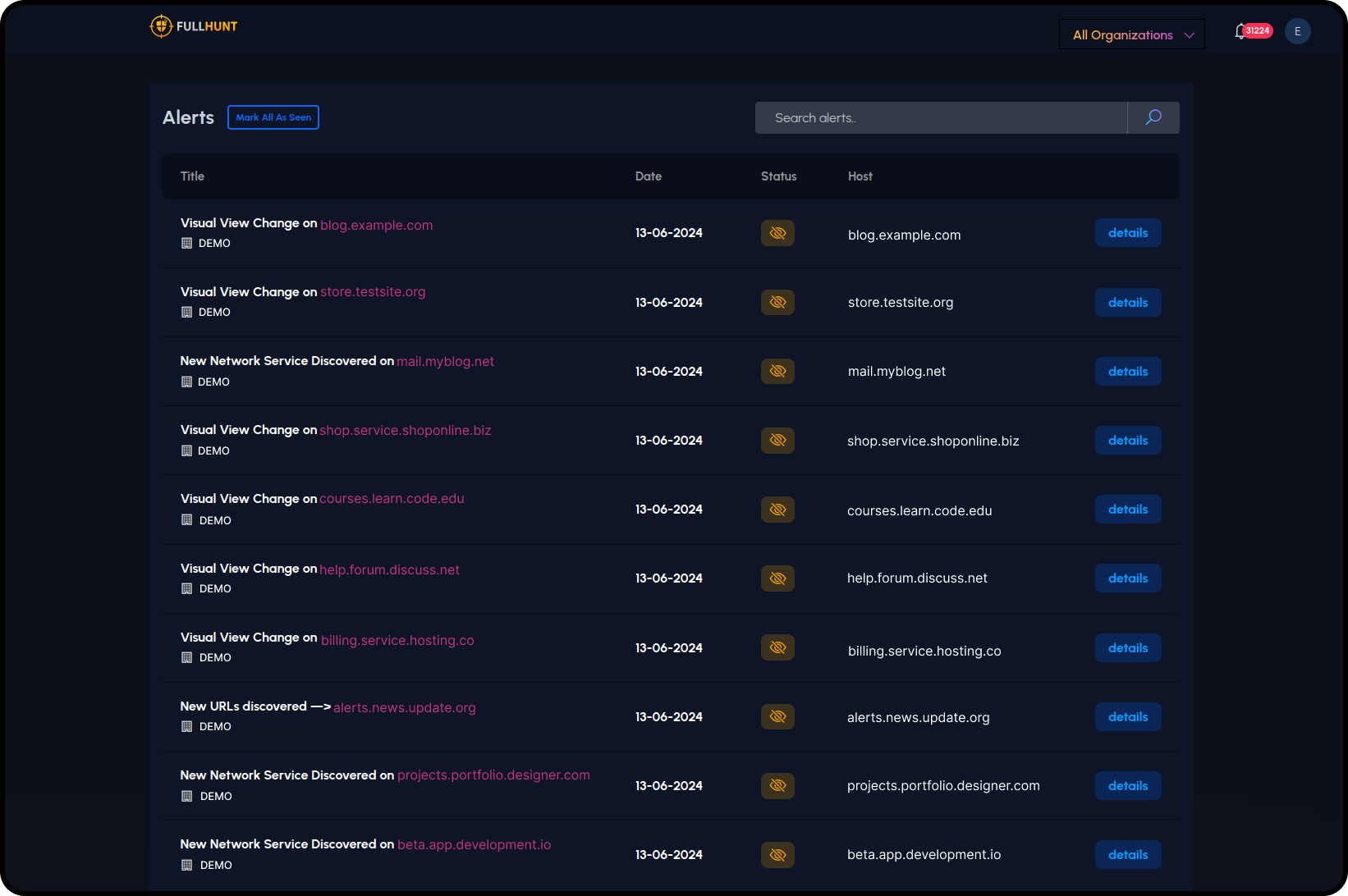
Know the moment your attack surface changes.
Real-time alerting on visual changes, new services, new URLs, and configuration drift. Every change is logged and attributed.
- — Visual change detection
- — New network services
- — New URLs & endpoints
- — Configuration drift alerts
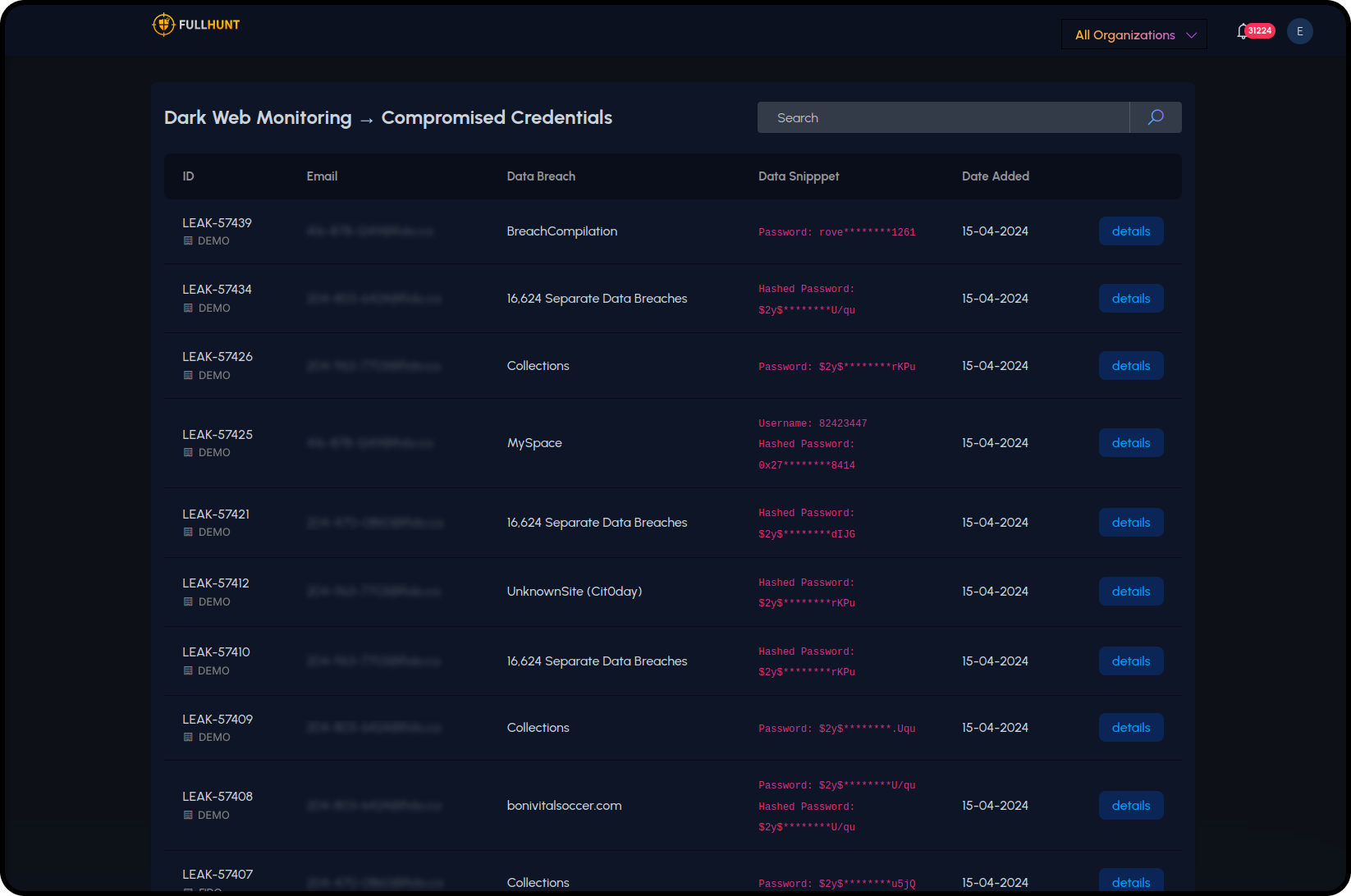
Visibility beyond your own perimeter.
Monitor your digital presence beyond the perimeter: employee credentials, brand abuse, and adversary infrastructure targeting your organization.
- — Compromised Credentials: employee accounts exposed in breaches and infostealer logs
- — Typosquatting Detection: monitor lookalike domains registered against your brand
- — Potential Phishing Infrastructure: identify adversary-controlled domains targeting your users
Every vulnerability validated. Prioritized by real-world risk.
4,000+ security checks run against live assets with runtime validation. Findings are enriched with exploit context, EPSS, and KEV data.
- — Expired SSL certificates
- — Misconfigurations
- — Local file inclusion
- — CVE-specific checks
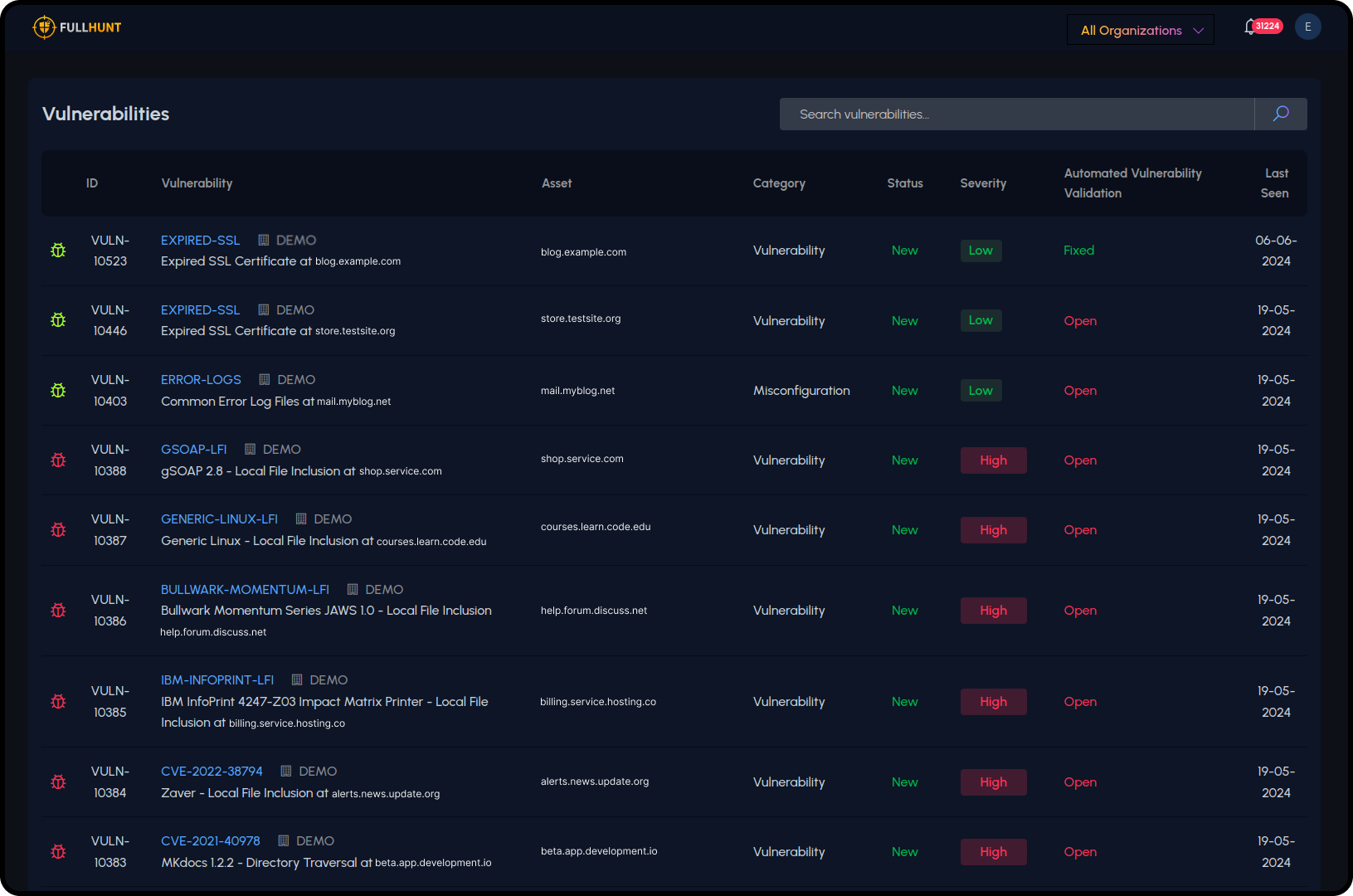
Prioritize what matters with exploit-aware intelligence.
Runtime-validated findings enriched with EPSS, KEV, and real-time exploit intelligence. No manual lookups. No separate tools.
- — 4,000+ runtime-validated vulnerability checks
- — EPSS probability scoring updated daily
- — CISA KEV active exploitation alerts
- — MCP & Agentic AI integrations
Why teams choose FullHunt for enterprise security
Full Coverage
Discovery, vulnerabilities, dark web, and exploit intelligence in one platform. No blind spots between tools.
Validated Findings
Runtime validation cuts false positives. Your team works on real issues, not noise.
AI-Powered
MCP server and agentic AI integrations let your AI workflows query attack surface data natively.
Fits Your Workflow
Push findings to Splunk, XSOAR, Jira, Slack, and more. No context switching.
See your full attack surface, starting today
Enterprise security teams use FullHunt to reduce blind spots, cut alert noise, and focus on real risk.