Nation-Scale Attack Surface Intelligence
Enumerate, enrich, and monitor internet-facing infrastructure at national scale. Bulk data access, passive DNS, organization attribution, and vulnerability intelligence, purpose-built for CERTs and government security programs.

Enumerate an entire nation's internet-facing footprint.
Continuous enumeration across all monitored organizations: government, critical infrastructure, and private sector. No agents, no network access required.
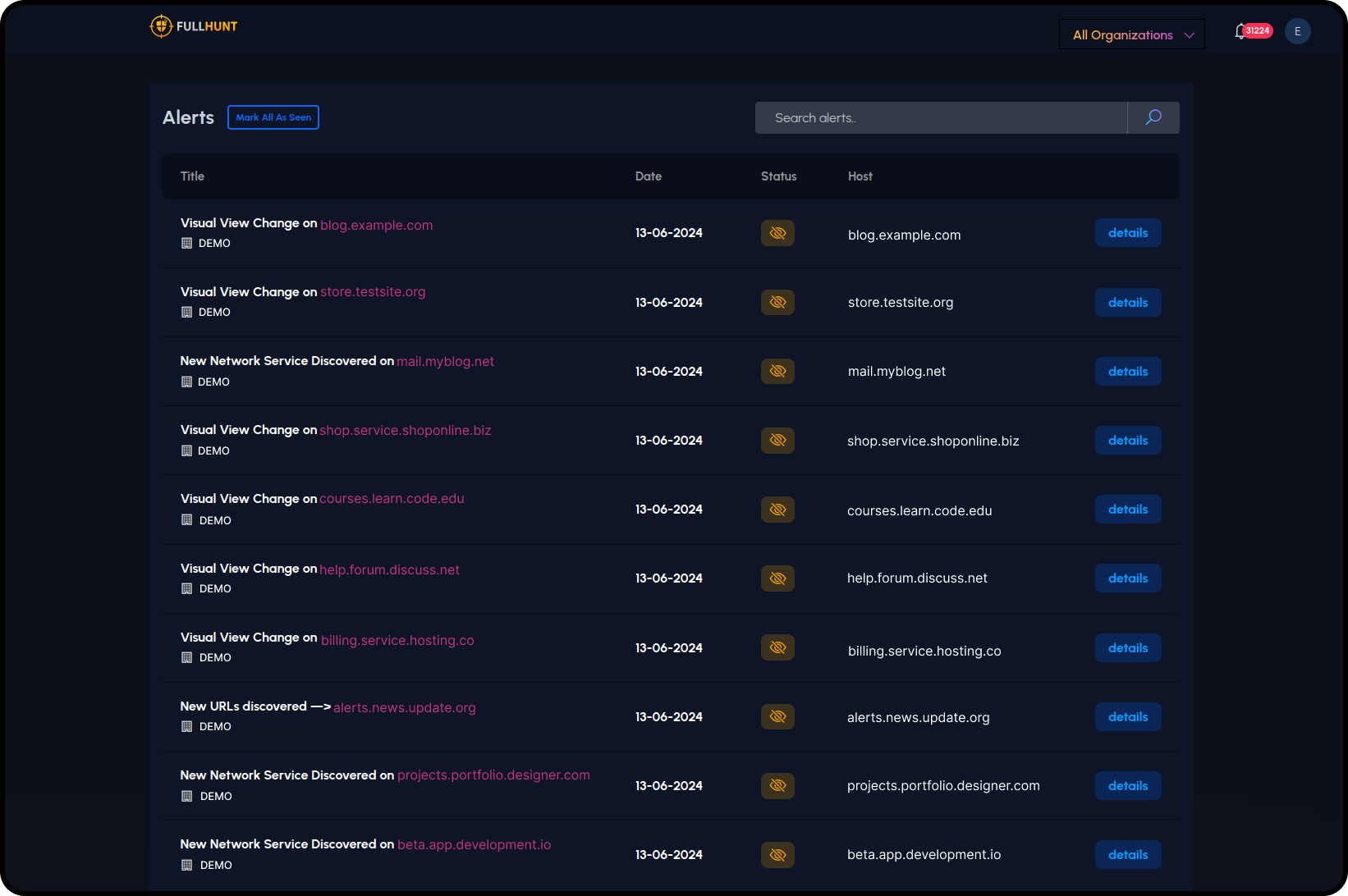
Detect changes across national infrastructure in real time.
Real-time alerting on visual changes, new services, new URLs, and configuration drift across all monitored organizations.
- — Visual change detection
- — New network services
- — New URLs & endpoints
- — Cross-sector alerts

Rich internet research data for threat hunting and attribution.
Access passive DNS history, TOR infrastructure, OSINT artifacts to support threat hunting, attribution, and incident response coordination.
- — Passive DNS: historical DNS resolution records for any domain or IP
- — Internet Research Data: TOR exit nodes, OSINT enrichment, research artifacts
- — Historical Data: track how assets and configurations change over time
- — On-Demand Scanning: trigger targeted scans for incident response or investigations
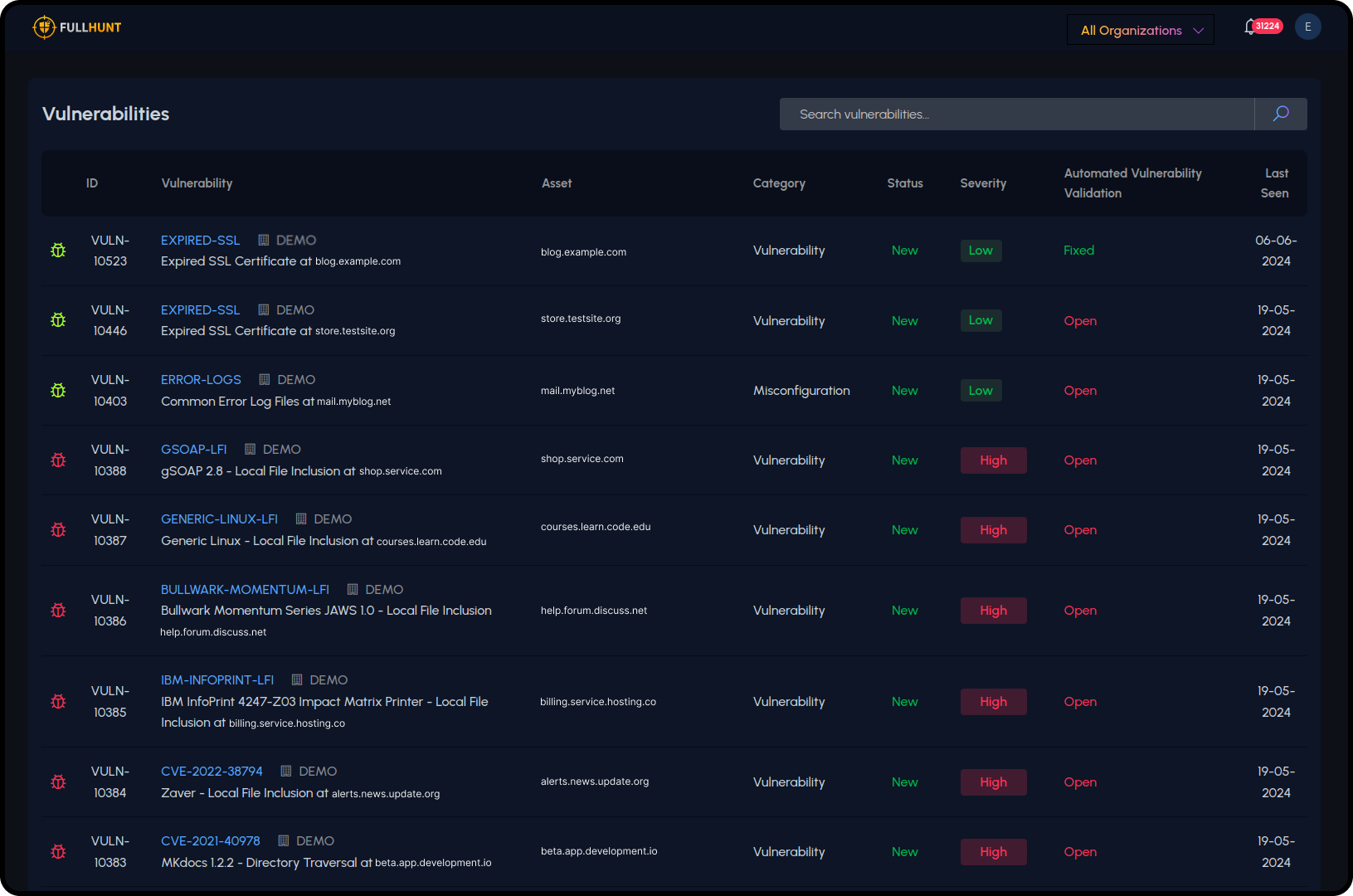
Track vulnerabilities across an entire nation's assets.
4,000+ security checks run against live assets with runtime validation. Map findings to organizations for coordinated response.
- — SSL/TLS issues
- — Misconfigurations
- — LFI/RFI checks
- — CVE-specific detections
Monitor CVE and exploit activity across national infrastructure.
Identify affected organizations and coordinate response before incidents escalate. Every CVE enriched with exploit context.
- — Full CVE database with EPSS and KEV enrichment
- — ML-driven exploit prediction updated daily
- — CISA KEV mapped to national assets
- — Organization-level impact mapping for coordinated disclosure

Why CERTs choose FullHunt
Nation-Scale Coverage
Enumerate and monitor internet-facing assets across an entire country's IP space continuously.
Bulk Data Access
REST APIs and bulk exports for integration with national security platforms and coordination tools.
Coordination-Ready
Map vulnerabilities to affected organizations for coordinated disclosure and sector-level advisories.
Research-Grade Data
Passive DNS, historical records, TOR data, and OSINT artifacts for threat research and attribution.
Protect your nation's internet-facing infrastructure
CERTs and government security teams use FullHunt for national-scale discovery, enrichment, and vulnerability coordination.