Build on FullHunt's Attack Surface Intelligence
Embed discovery, enrichment, vulnerability intelligence, and agentic AI in your product. No scanners to build, no infrastructure to maintain. Ship security features in weeks.

Add host and domain intelligence to your product with a single API call.
No scanning infrastructure required. Enrichment, attack path analysis, and IP lookup via clean REST APIs.
Native AI integration for your security platform.
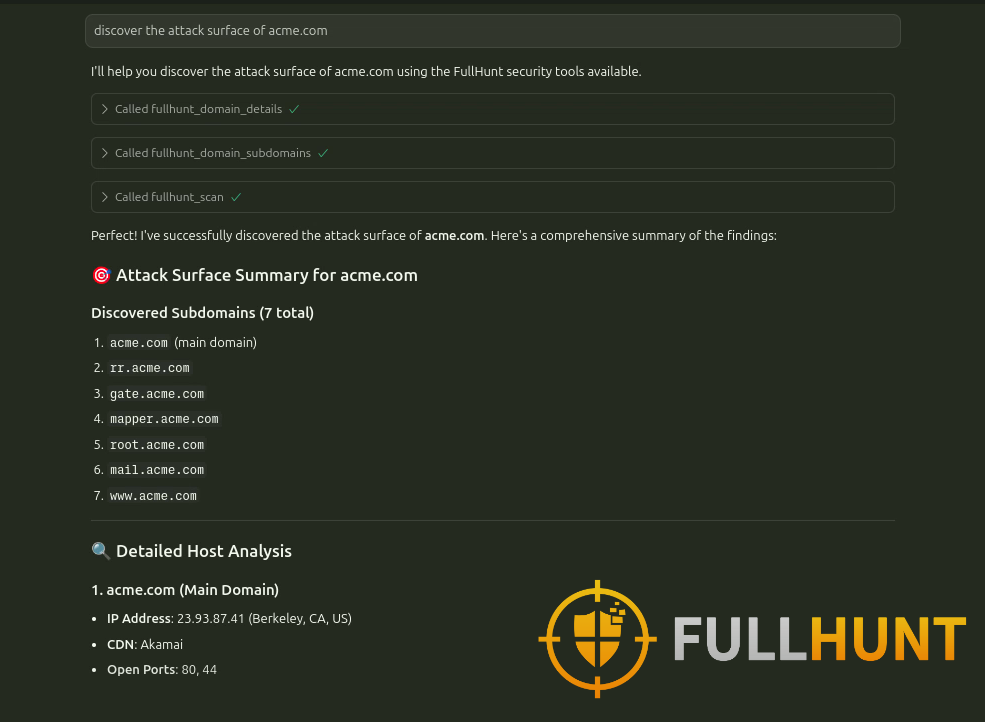
Connect FullHunt to any AI agent framework via our native MCP server. Let your AI security workflows query attack surface data, enrichment, and threat intelligence natively.
- — MCP & Agentic AI: native MCP server compatible with Claude, GPT, and other agent frameworks
- — Structured API responses: clean JSON optimized for LLM consumption
- — Real-time queries: always-fresh data for agentic workflows
The full intelligence data catalog, via REST API.
Vulnerability and exploit databases, passive DNS history, TOR data, and historical records. All accessible programmatically.
Why security vendors choose FullHunt
White-Label Ready
Embed APIs under your brand. No attribution required. Your product, your data layer.
Fast Time-to-Market
Ship attack surface features in weeks, not months. No scanning infrastructure to build or maintain.
No Infrastructure
Zero scanners, zero crawlers, zero maintenance. FullHunt handles the data pipeline end-to-end.
Full Data Catalog
Enrichment, vulnerabilities, exploits, DNS, historical data, all from one vendor with one API key.
Build on FullHunt's attack surface intelligence
ISVs and security platforms embed FullHunt APIs to ship discovery, enrichment, and intelligence features, without building scanning infrastructure.